7 CIA Secrets Revealed in WikiLeaks “Vault7”
A week ago WikiLeaks began the release of “Vault7”, a series of leaks they have termed “the largest ever publication of confidential documents” on the US Central Intelligence Agency (CIA). The first part of the series, named “Year Zero”, is comprised of 8,761 documents and files captured from “an isolated, high-security network situated inside the CIA’s Center For Cyber Intelligence in Langley, Virginia”. And we’ve been told there’s much more to come. According to WikiLeaks’ official Twitter account the “Year Zero” publication comprises < 1% of the total information contained within the entire “Vault7” series!
“Vault7 – Year Zero” paints a dark picture of an enormous cyber intelligence community within the CIA possessed with near god-like powers in the digital domain. Contained within the files is evidence of everything from malware creation and mass-distribution into the public domain to smart TV’s being used as bugs in true Orwellian nightmare fashion. Indeed, it seems that the CIA is (or can be) everywhere.
Here are 7 of the most shocking secrets unsealed from WikiLeaks’ Vault7 “Year Zero”
1. The CIA has an in-house malware factory
In a press release accompanying the “Vault 7” files, WikiLeaks asserts that the CIA’s hacking division is enormous with a size and scope rivaling that of the NSA. The division falls under the agency’s Center for Cyber Intelligence (CCI) and had over 5000 registered users as of 2016. The division has produced a veritable arsenal of “more than a thousand hacking systems, trojans, viruses, and other “weaponized” malware”.
The CIA’s malware and hacking tools are built by a group within the CCI called the Engineering Development Group (EDG). The EDG is “responsible for the development, testing and operational support of all backdoors, exploits, malicious payloads, trojans, viruses and any other kind of malware used by the CIA in its covert operations world-wide”.
An organizational chart of the CIA can be viewed here
2. The CIA has the ability to carry out “false-flag” cyber-attacks
Not all of the hacking tools used by the agency are internally created. The CIA’s Remote Devices Branch‘s UMBRAGE group group maintains a collection of attack techniques lifted from malware programs created by other states. This data can then be used to plant the digital “fingerprints” of someone other than the CIA onto cyber-attacks for which the agency is actually responsible.
“With UMBRAGE and related projects the CIA cannot only increase its total number of attack types but also misdirect attribution by leaving behind the “fingerprints” of the groups that the attack techniques were stolen from” – WikiLeaks –
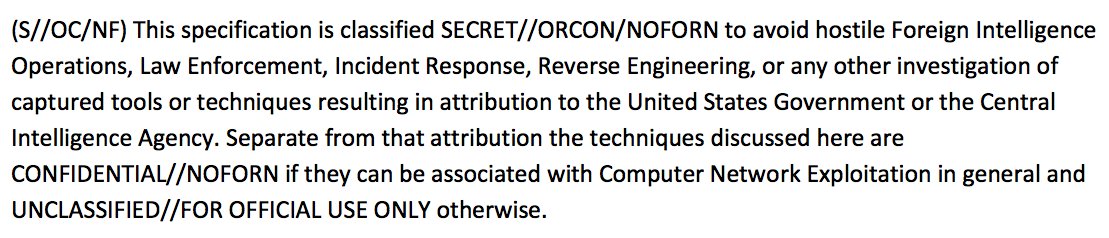
The “Vault7” leaks contain ample evidence that the CIA goes to great lengths to cover their cyber tracks. A lengthy guideline to best practices for writing agency malware is found in “Tradecraft DO’s and DON’Ts” . The list details methods to ensure that none of the digital actions taken by the CIA will possess any hallmarks of the agency itself. These methods are designed to both conseal the location from which the attack originated and to prevent forensic investigators from identifying the methods used. Thus, if an attempt is made to reverse-engineer a malware attack by the CIA, authorship of the hack would be extremely difficult to determine, or could be attributed to another source entirely. I.e. The CIA has the capacity to commit “false-flag” cyber attacks by framing another intelligence agency/state.
3. The CIA developed numerous attacks to remotely hack and control popular smart phones

The CIA has spent billions of dollars finding ways to gain access to the wealth of personal data contained on smart phones world-wide. The agency has specialized units within its Mobile Development Branch (MDB) dedicated to hacking both Apple and Android smart phones. iPhones and other products which run iOS such as iPads, have been targeted with malware capable of taking control of the device and subsequently exfiltrating the users personal data. The CIA may then gain access to information such as geolocation, audio and text communications, and may even covertly activate the device’s microphone or camera.
Google’s Android products have been similarly targeted by a similar unit and, as of last year, the CIA had 24 “weaponized” Android “zero days” (vulnerabilities in a software platform that are unknown to the manufacturer) which it has either developed itself or obtained from GCHQ, NSA and cyber arms contractors.
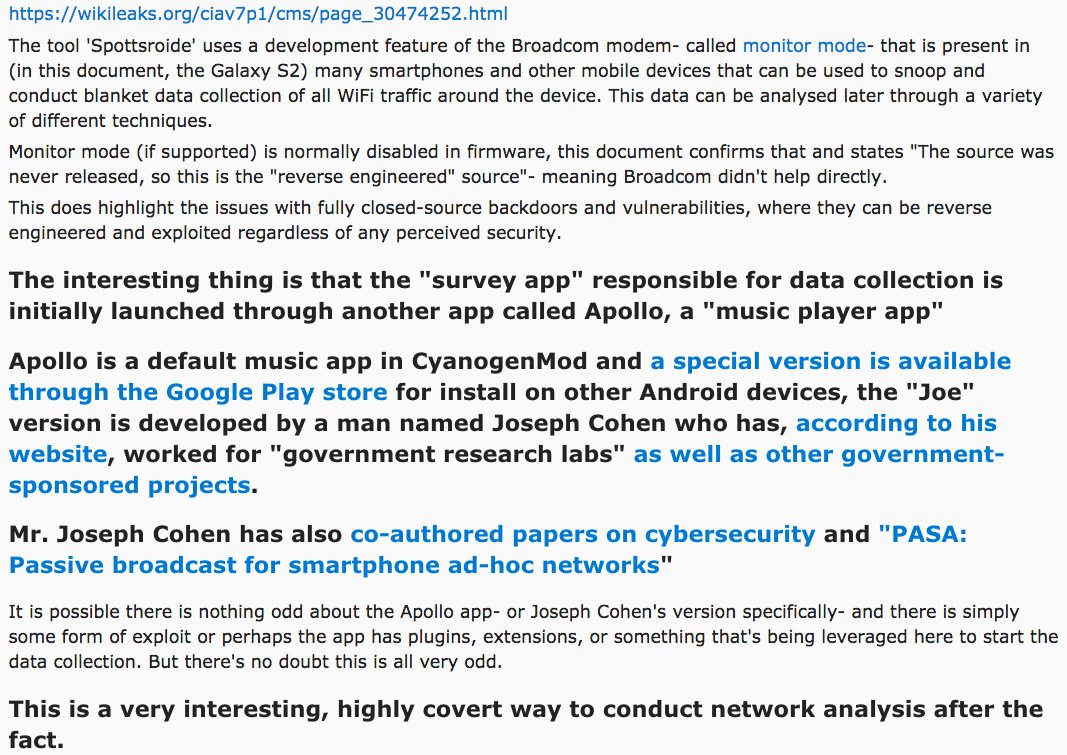
The agency’s attacks on Android go much further as “Vault7” contains evidence that the CIA developed a tool to turn Android devices into bulk-data collectors of any WiFi traffic in the vicinity of the target device.
4. The US Consulate in Frankfurt serves as a covert CIA hacker base
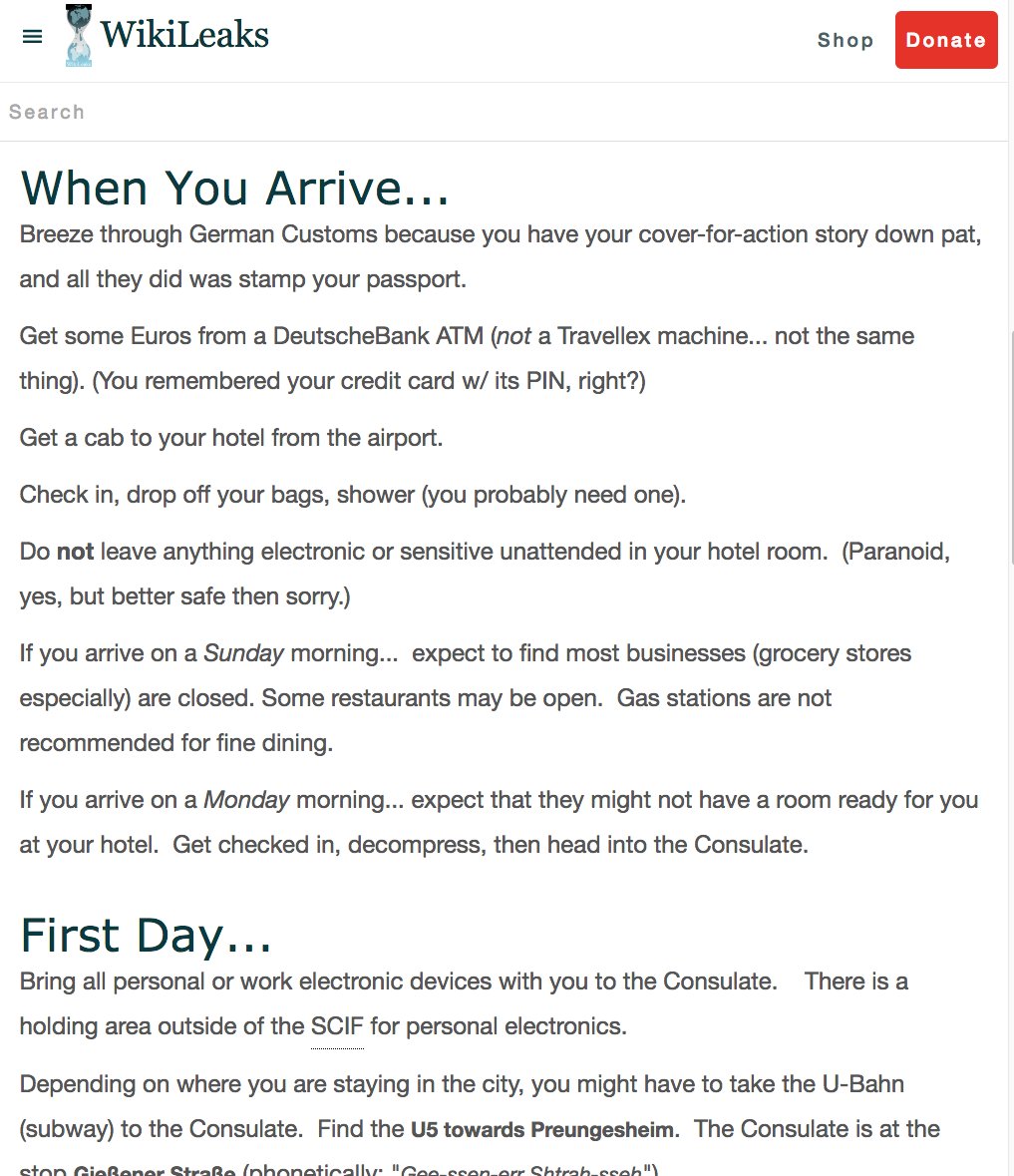
The CIA’s hacking division personnel aren’t confined to the Langley, VA campus. Documents provided in “Vault7” indicate that the US Consulate in Frankfurt Germany has been used as a base for CIA hacking operations abroad. Agency hackers are given diplomatic passports and State Department cover. After arriving in Frankfurt, they can then travel without further border checks to the 25 European countries that are part of the Shengen open border area — including France, Italy and Switzerland. Below is an instruction sheet for new arrivals.
WikiLeaks further states that the CIA has numerous electronic attack methods which are “designed for physical proximity” so as to gain access to high-security networks not connected to the internet. These methods involve a CIA officer physically infiltrating an area and stealing information through insertion of a malware-containing USB device into a target computer system.
“The attacker then infects and exfiltrates data to removable media. For example, the CIA attack system Fine Dining, provides 24 decoy applications for CIA spies to use. To witnesses, the spy appears to be running a program showing videos (e.g VLC), presenting slides (Prezi), playing a computer game (Breakout2, 2048) or even running a fake virus scanner (Kaspersky, McAfee, Sophos). But while the decoy application is on the screen, the underlaying system is automatically infected and ransacked.” – WikiLeaks –
The implication here is that the CIA has the ability to insert officers into friendly countries using the Frankfurt Consulate as a base of operations. Traveling under the guise of working for the State Department as technical consultants, agents could then gain access to any number of highly restricted computer networks and plant malware and/or exfiltrate sensitive data.
The German government is taking this information seriously. A spokesman for Germany’s chief federal prosecutor said, “We will initiate an investigation if we see evidence of concrete criminal acts or specific perpetrators,” a spokesman for the federal prosecutor’s office said. “We’re looking at it very carefully.”
The German government has good reason to be concerned by this revelation. After all, Barack Obama had authorized the monitoring of Chancellor Angela Merkel’s mobile phone in 2010. Intelligence leaks also showed that the US conducted eavesdropping operations on the German government from a listening post at its embassy beside the Brandenburg Gate in Berlin.
America has history of spying on friends and allies, so it’s not unreasonable to suspect that the CIA’s malware attacks requiring “physical-proximity”would likely be used against allied nations.
5. Windows and other operating systems have “gaping security holes” the CIA is exploiting

According to WikiLeaks, the CIA aggressively seeks to “infect and control” Microsoft Windows user’s systems with malware. A variety of methods are used to gain access including multiple local and remote weaponized “zero days”, air gap jumping viruses such as “Hammer Drill” which infects software distributed on CD/DVDs, infectors for removable media such as USBs, systems to hide data in images or in covert disk areas ( “Brutal Kangaroo”) and to keep its malware infestations going.
The agency has developed a multi-platform malware suite called HIVE which provides customizable implants for operating systems like Windows, Linux, Solaris, and MikroTik which is used in internet routers. The project also provides a Listening Post (LP)/Command and Control (C2) infrastructure to communicate with these implants.
It should be noted that in 2010 the Obama administration made a commitment to the US technology industry that pervasive vulnerabilities found in operating systems would be disclosed to manufacturers on an ongoing basis.
It appears that didn’t happen.
The “Vault7-Year Zero” release reveals that the CIA breached the Obama administration’s commitment to the Vulnerabilities Equities Process by hoarding knowledge of these “zero day” vulnerabilities. WikiLeaks asserts that “some may already have been found by rival intelligence agencies or cyber criminals”. By allowing these pervasive “zero day” vulnerabilities to remain undisclosed to manufacturers, the CIA has knowlingly placed everyone using these systems at risk.
6. Smart TVs can be used as listening devices
Seemingly taking inspiration right from the dystopian pages of George Orwell’s 1984, the CIA developed a malware program which can infest Samsung smart TVs and turn them into covert listening devices. The project, code-named “Weeping Angel”, was developed by the CIA’s Embedded Devices Branch (EDB) in concert with the United Kingdom’s MI5/BTSS. After being infested with the “Weeping Angel” malware, the TV can be placed in a “Fake-Off” mode and used as a bug. Though it appears to the owner that the power is off, the power secretly remains on and the TV’s microphone is then used to covertly record conversations in the room. Any audio obtained while the TV is in “Fake-Off” mode is then sent to a covert CIA server.
7. The CIA’s hacking arsenal is largely unclassified and running loose in the public domain
The CIA’s weaponized malware (implants + zero days), Listening Posts (LP), and Command and Control (C2) systems are all unclassified. The reasoning behind this is that most CIA malware implants must communicate with their control programs via the internet. Therefore, if the programs were classified, CIA officers could be dismissed or even prosecuted for transmitting classified information on the internet.
In order to get around US Federal laws regarding classified materials, these weapons must be released as unclassified, essentially placing them into the public domain. This in turn creates the opportunity for any number of hackers and/or hostile entities to freely pirate and use these weapons if they are obtained with little recourse available to the CIA, or US federal governtment.
The CIA has in essence created a cyber nuclear arsenal which it has no effective way of securing or maintaining control over.
WikiLeaks’ “Vault7 – Year Zero” release is perhaps the organization’s most important series of leaks to date. It provides confirmation that the powers-that-be have a standing army of consumer electronic devices ready to capture video, record audio, and obtain whatever information they desire about anyone deemed a “target” by the CIA.
Americans, ask yourselves, what is the true intent of these massive CIA programs? Is the intent to keep us safe? Or is the intent to give the government near unfiltered access to our private lives, further chilling free thought and speech?
WikiLeaks “Vault7 – Year Zero” release confirms what many have long suspected – the US government has a nearly omniscient presence in the digital domain.
The majority of us now have lives which are largely carried out through electronic devices and catalogued in the digital domain. The CIA now sits atop a digital Mount Olympus with an arsenal of information-gathering weapons; An all-seeing eye intent on monitoring whatever we do in private with the aim of controlling what we do in public.
Ask yourself, is there anyone you would trust with that kind of power?






